- Defend & Conquer
- Posts
- Key design principles for implementing security architecture review boards in agile software delivery methodologies
Key design principles for implementing security architecture review boards in agile software delivery methodologies
CybersecurityHQ Report - Pro Members

Welcome reader to a 🔒 pro subscriber-only deep dive 🔒.
Brought to you by:
👣 Smallstep – Secures Wi-Fi, VPNs, ZTNA, SaaS and APIs with hardware-bound credentials powered by ACME Device Attestation
🏄♀️ Upwind Security – Real-time cloud security that connects runtime to build-time to stop threats and boost DevSecOps productivity
🔧 Endor Labs – App security from legacy C++ to Bazel monorepos, with reachability-based risk detection and fix suggestions across the SDLC
📊 LockThreat – AI-powered GRC that replaces legacy tools and unifies compliance, risk, audit and vendor management in one platform
🧠 Ridge Security – The AI-powered offensive security validation platform
Forwarded this email? Join 70,000 weekly readers by signing up now.
#OpenToWork? Try our AI Resume Builder to boost your chances of getting hired!
—
Get lifetime access to our deep dives, weekly cyber intel podcast report, premium content, AI Resume Builder, and more — all for just $799. Corporate plans are now available too.
Executive Summary
Security Architecture Review Boards (SARBs) face a fundamental challenge in 2025: maintaining robust security governance while enabling the rapid innovation that agile methodologies demand. Traditional review boards, with their sequential approval processes and heavyweight documentation requirements, create bottlenecks that undermine agile principles. Yet the need for architectural security oversight has never been greater, with organizations facing sophisticated AI-driven threats, zero trust mandates, and complex regulatory requirements.

Our analysis reveals that successful SARBs in agile environments share five key design principles. First, they embed security expertise directly within agile teams through dedicated roles like security champions and security developers. Second, they leverage extensive automation, with some organizations reducing review times from weeks to hours through policy-as-code and automated compliance checking. Third, they integrate security activities into existing agile ceremonies rather than creating separate processes. Fourth, they implement adaptive governance models that balance team autonomy with organizational control based on risk levels and team maturity. Fifth, they adopt modular, information-centric approaches tailored to specific operational contexts.
The evidence shows these principles work. Organizations implementing automated review processes report review time reductions of up to 95%. Those embedding security roles within teams see faster identification and resolution of security issues. Companies using adaptive governance models maintain security standards while preserving development velocity. Large enterprises lead in adoption, with organizations over $500 million in revenue twice as likely to have implemented dedicated security architecture teams and automated review processes.
Looking forward, SARBs must evolve to address emerging challenges including AI system security, cloud-native architectures, and zero trust implementations. Success requires treating security architecture governance not as a gate to pass but as an enabler of secure innovation.
/
Introduction: The Evolution of Security Architecture Governance
The traditional Security Architecture Review Board emerged from an era of waterfall development, lengthy release cycles, and monolithic applications. These boards operated as checkpoints, reviewing detailed architecture documents and granting approvals before development could proceed. This model served its purpose when software releases happened quarterly or annually, and architectures remained relatively stable between releases.
Today's reality is fundamentally different. Organizations deploy code multiple times daily, architectures evolve continuously, and development teams expect autonomy to make rapid decisions. The 2025 technology landscape adds new complexity: AI-driven attacks that adapt in real-time, supply chain vulnerabilities that cascade across ecosystems, and regulatory requirements that demand both agility and compliance.
This transformation has created a crisis of relevance for traditional SARBs. Teams bypass review processes they perceive as obstacles, creating shadow IT and technical debt. Security teams struggle to keep pace with development velocity, often discovering issues only after deployment. The result is a lose-lose scenario: security governance that neither enables business agility nor effectively manages risk.
Yet the core mission of security architecture review remains vital. Design-level security flaws are exponentially more expensive to fix after implementation. Architectural decisions about authentication, data flow, and network segmentation have lasting security implications. Regulatory compliance increasingly requires demonstrable security-by-design practices.
The solution lies not in abandoning security architecture governance but in fundamentally reimagining how it operates. Modern SARBs must transform from gatekeepers to enablers, from reviewers to embedded partners, from document-focused to automation-driven. This transformation requires new principles, practices, and technologies.
This white paper examines how leading organizations are successfully integrating security architecture review with agile delivery. Drawing on empirical research, case studies, and emerging practices, we identify the key design principles that enable SARBs to provide effective governance without impeding agility. We explore how automation, embedded expertise, and adaptive models create security architecture review processes that enhance rather than hinder rapid delivery.
The Current State: Challenges and Opportunities
The Agile-Security Tension
Agile methodologies prioritize individuals and interactions over processes and tools, working software over comprehensive documentation, customer collaboration over contract negotiation, and responding to change over following plans. Traditional security architecture review practices violate each of these principles: they emphasize formal processes, require extensive documentation, operate through governance contracts, and resist change to approved architectures.
This fundamental misalignment creates practical challenges. Agile teams operating in two-week sprints cannot wait weeks for architecture approval. Developers focused on delivering working software resist creating detailed design documents for review. Teams empowered to make decisions feel constrained by centralized approval requirements. The iterative nature of agile development means architectures evolve continuously, making point-in-time reviews obsolete.
Research confirms these tensions are widespread. Studies show that security architecture review ranks among the top impediments to agile delivery. Teams report delays averaging three to six weeks for security architecture approval. Many organizations experience shadow IT growth as teams circumvent review processes perceived as blocking progress.
Emerging Opportunities
Despite these challenges, several trends create opportunities for effective integration. DevSecOps practices demonstrate that security can be embedded throughout the development lifecycle. Infrastructure as Code enables policy enforcement through automation. Cloud-native architectures provide programmatic security controls. AI and machine learning offer new possibilities for continuous architecture analysis.
Organizations are discovering that agile principles, properly applied, can enhance security architecture governance. Frequent iterations enable continuous security improvement. Cross-functional teams bring security expertise directly into development. Automated testing allows rapid security validation. Short feedback loops enable quick identification and resolution of architectural security issues.
The shift from project-based to product-based development models also creates opportunities. Product teams maintaining long-term ownership have stronger incentives to build secure architectures. Continuous delivery pipelines provide natural integration points for security controls. Platform engineering approaches enable centralized security capabilities with decentralized consumption.
Industry-Specific Contexts
Different industries face unique challenges and opportunities in integrating security architecture review with agile delivery. Financial services organizations must balance innovation with strict regulatory requirements like PCI DSS and Basel III. Healthcare providers navigate HIPAA compliance while modernizing patient care systems. Government agencies implement zero trust architectures while adopting agile practices. Technology companies push the boundaries of rapid delivery while managing complex distributed systems.
These industry contexts shape how organizations approach security architecture governance. Banks often maintain formal review boards but streamline processes through automation and delegation. Healthcare organizations emphasize privacy-by-design reviews integrated with security assessments. Government agencies leverage reference architectures and automated compliance checking. Technology companies embed security architecture decisions within platform teams and developer tools.
Understanding these contextual differences is crucial for designing effective security architecture review processes. What works for a regulated financial institution may not suit a fast-moving startup. What serves a government agency may not fit a healthcare provider. Successful approaches adapt core principles to specific organizational contexts.
Key Design Principles

Principle 1: Embedded Security Expertise

The most fundamental shift in modern security architecture review is moving expertise from centralized boards into development teams. This embedded model takes various forms but shares a common philosophy: security architecture decisions happen where and when development occurs, not in separate review meetings weeks later.
Security champions represent the most common embedded model. These team members receive specialized training in security architecture principles and serve as the first line of review for design decisions. They participate in sprint planning, design sessions, and code reviews, providing real-time security input. Champions maintain connections to central security architecture teams, escalating complex issues and sharing learnings across the organization.
Some organizations go further with dedicated security developer roles. These individuals combine development skills with security expertise, writing secure code while guiding architectural decisions. Security developers often own security-critical components like authentication services or encryption libraries, ensuring these foundational elements meet architectural standards.
The embedded model extends to collaborative practices. Rather than submitting designs for review, teams engage security architects in design sessions. Instead of documenting architectures for approval, teams demonstrate security through automated tests and compliance scans. This shift from review to collaboration fundamentally changes the dynamic between security and development teams.
Research demonstrates the effectiveness of embedded expertise. Organizations with security champions report faster identification of security issues, with problems caught during design rather than testing. Teams with embedded security developers show higher adoption of secure coding practices and architectural patterns. Collaborative design sessions result in more secure and implementable architectures.
Implementing embedded expertise requires investment in people and processes. Organizations must identify and train champions, create career paths for security developers, and establish collaboration frameworks. Central security teams must shift from reviewers to coaches and enablers. Success depends on creating incentives for security engagement and recognizing security contributions alongside feature delivery.
Principle 2: Automation-Driven Governance
Manual review processes cannot scale with agile delivery velocity. Organizations deploying multiple times daily need security architecture governance that operates at the speed of automation. This shift from human review to automated validation represents a fundamental change in how security architecture review boards operate.
Policy-as-code forms the foundation of automated governance. Security architecture standards translate into executable rules that validate infrastructure configurations, application designs, and deployment patterns. These policies run continuously in development pipelines, providing immediate feedback on architectural compliance. Teams know within minutes, not weeks, whether their designs meet security standards.
Infrastructure as Code enables this automation by making architecture decisions explicit and versionable. Security policies validate Terraform configurations for network segmentation, Kubernetes manifests for container isolation, and CloudFormation templates for encryption settings. Version control provides audit trails of architectural decisions and policy evolution.
Automated architecture analysis goes beyond configuration checking. Tools generate dependency graphs from code repositories, identifying unauthorized connections between components. Service mesh configurations enforce zero trust principles through policy rather than manual review. API gateways validate that exposed interfaces follow security patterns. Machine learning models identify anomalous architectural patterns that might indicate security issues.
The impact of automation on review velocity is dramatic. Organizations report reducing review times from weeks to hours. Some achieve near-instantaneous validation for standard patterns, requiring human review only for exceptions. This speed enables true continuous delivery while maintaining security governance.
Successful automation requires thoughtful implementation. Policies must balance security requirements with development flexibility. Automated checks need clear error messages and remediation guidance. Override mechanisms must exist for legitimate exceptions with appropriate authorization and audit trails. Tools must integrate seamlessly with existing development workflows to encourage adoption.
Principle 3: Agile Ceremony Integration
Security architecture review succeeds when it becomes part of agile workflows rather than a separate process. This integration happens through existing ceremonies and artifacts that teams already use, adding security perspectives without adding meetings or documentation.
Sprint planning provides natural opportunities for security architecture input. As teams discuss upcoming work, security champions or architects identify items requiring architectural consideration. User stories include security acceptance criteria alongside functional requirements. Architecture spikes address security concerns within the sprint rather than through separate review cycles.
Daily standups surface security architecture impediments alongside other blockers. Teams discuss security design challenges and get immediate input from embedded experts or connected architects. This continuous engagement prevents security issues from accumulating into major problems requiring formal review.
Sprint reviews demonstrate security architecture implementation through working software rather than documents. Teams show how authentication flows work, how data encryption operates, and how network segmentation functions. Security architects see actual implementations rather than theoretical designs, enabling more practical feedback.
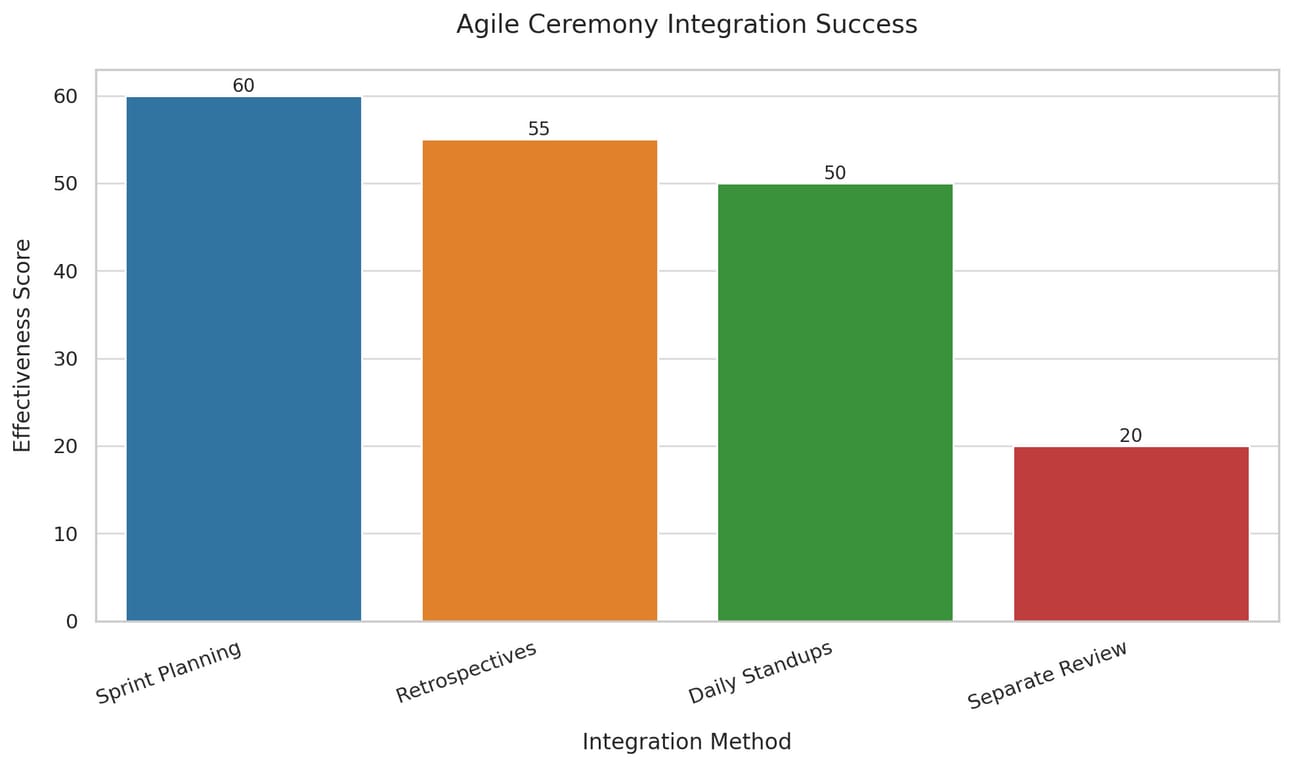
Retrospectives create opportunities for continuous improvement in security architecture practices. Teams reflect on what security patterns worked well and what created friction. They identify opportunities to improve security integration and adjust practices for future sprints. This iterative refinement helps security architecture governance evolve with team needs.
Backlog refinement sessions incorporate security architecture requirements into upcoming work. Security experts help teams understand the architectural implications of proposed features. They identify necessary security patterns and help estimate implementation effort. This proactive engagement ensures security architecture considerations inform planning rather than surprising teams later.
The effectiveness of ceremony integration depends on security participants understanding agile practices and contributing constructively. Security experts must speak the language of user stories and acceptance criteria. They must provide input that enables progress rather than creating impediments. Success requires security professionals who embrace agile principles while maintaining security standards.
Principle 4: Risk-Adaptive Governance
Not all architectural decisions carry equal security risk. Effective security architecture review boards recognize this reality through adaptive governance models that match oversight intensity to risk levels. This risk-based approach enables teams to move quickly on low-risk changes while ensuring appropriate scrutiny for critical decisions.
Risk assessment begins with clear categorization frameworks. High-risk changes might include new external interfaces, modifications to authentication systems, or handling of sensitive data. Medium-risk changes could involve internal service modifications or standard pattern implementations. Low-risk changes might be updates to existing components within established security boundaries.
Governance intensity adapts to these risk levels. High-risk changes receive full security architecture review with detailed threat modeling and formal approval. Medium-risk changes undergo lightweight review through automated checking and champion validation. Low-risk changes proceed with standard automated controls and post-implementation monitoring.
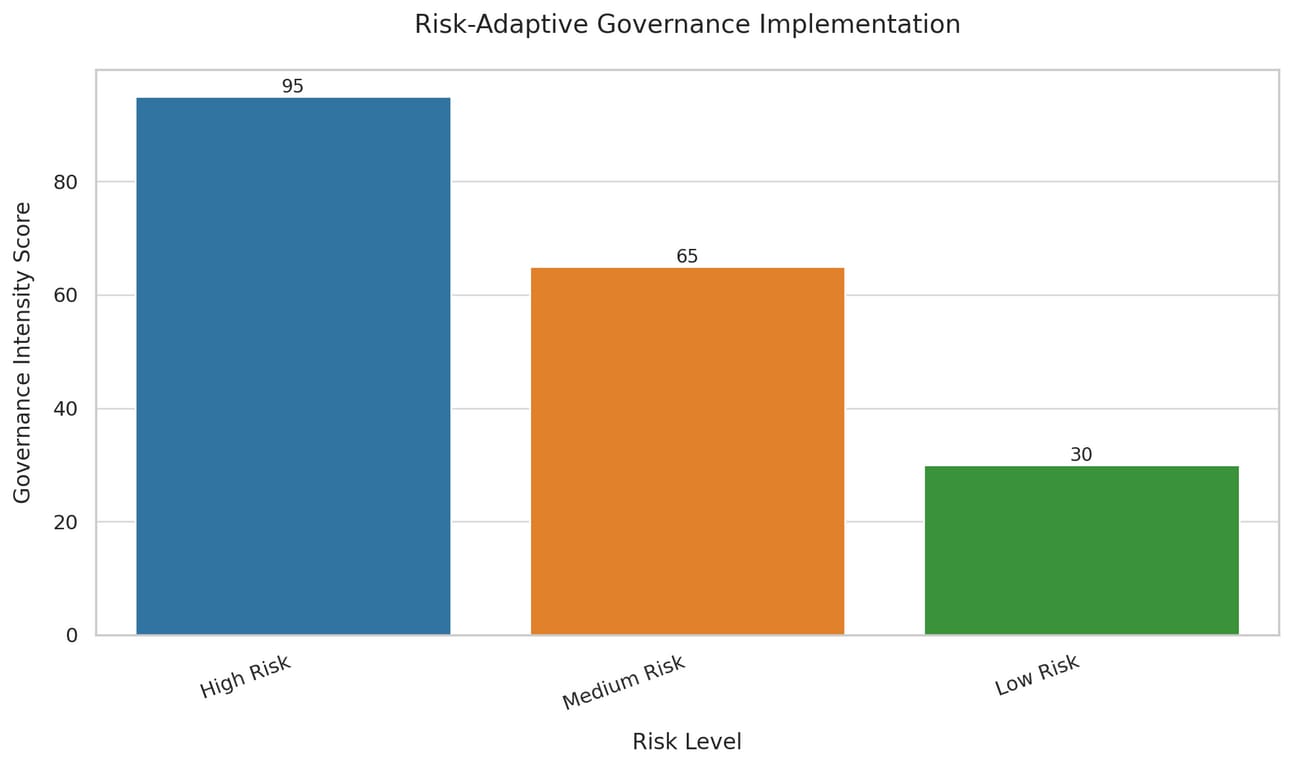
Team maturity factors into governance adaptation. Experienced teams with strong security track records receive greater autonomy. New teams or those with past security issues face more oversight. This graduated approach incentivizes security excellence while providing support where needed.
Context influences risk assessment and governance needs. A proof-of-concept in a development environment faces different requirements than production deployment. Internal tools have different risk profiles than customer-facing services. Regulated data requires stricter governance than public information. Effective boards calibrate their involvement to these contextual factors.
Dynamic adjustment keeps governance relevant as conditions change. Teams earning trust through consistent security excellence graduate to lighter oversight. Emerging threats trigger temporary increases in review intensity for affected areas. New regulations prompt updates to risk categories and governance requirements. This adaptability ensures governance remains effective without becoming rigid.
Implementing adaptive governance requires clear frameworks and consistent application. Teams need transparent criteria for risk categorization and governance requirements. Escalation paths must exist for borderline cases. Regular calibration ensures risk assessments remain accurate and governance levels appropriate. Success depends on maintaining objectivity while enabling flexibility.
Principle 5: Continuous Validation
Traditional security architecture review operates as a point-in-time assessment. Architectures receive approval based on design documents, then drift from approved states through incremental changes. Modern security architecture governance recognizes that architectures evolve continuously and require ongoing validation.
Continuous validation begins with runtime verification. Production systems generate telemetry confirming that architectural security controls function as designed. Network flows validate segmentation policies. Authentication logs confirm identity requirements. Encryption metrics verify data protection. This operational data provides ground truth about actual versus intended architecture.
Architecture drift detection identifies when systems deviate from approved patterns. Automated tools compare running configurations against approved baselines, flagging unauthorized changes. Service discovery mechanisms detect new components or connections requiring security review. Configuration management databases track architectural evolution, triggering reviews for significant changes.
Feedback loops connect operational insights to architecture governance. Security incidents reveal architectural weaknesses requiring design updates. Performance metrics identify security controls creating bottlenecks. Compliance audits surface gaps between documented and actual architectures. These insights drive continuous architectural improvement rather than one-time fixes.
Predictive analysis anticipates architectural security issues before they manifest. Machine learning models identify patterns associated with future vulnerabilities. Dependency analysis reveals components approaching end-of-life requiring architectural updates. Threat intelligence informs proactive architectural hardening against emerging attack patterns.
Continuous improvement processes embed architectural learning throughout the organization. Post-incident reviews identify architectural contributors to security events. Success stories share effective security patterns across teams. Regular architecture reviews refresh standards based on evolving threats and technologies. This learning orientation ensures architecture governance improves over time.
Implementing continuous validation requires investment in monitoring and analysis capabilities. Organizations need comprehensive telemetry collection and processing infrastructure. Teams need dashboards visualizing architectural security status. Processes must exist for translating insights into governance updates. Success depends on creating actionable feedback that improves both architectures and governance processes.
Implementation Strategies
Organizational Design for Modern SARBs
The structure of security architecture review boards must evolve to support agile delivery. Traditional hierarchical committees give way to networked models that distribute expertise while maintaining coherence. This organizational evolution reflects broader transformations in how enterprises coordinate complex activities.
Hub and spoke models balance centralization with distribution. A central security architecture team maintains standards, develops automation, and handles complex reviews. Distributed security architects or champions embed within product teams, providing local expertise and escalating issues when needed. This structure provides consistency while enabling rapid local decision-making.
Community of practice approaches foster peer learning and standard evolution. Security architects, champions, and interested developers form communities that share experiences and develop practices. These communities create forums for discussing architectural patterns, solving common problems, and evolving standards based on practical experience.
Governance boards evolve from approval bodies to enabling functions. Rather than reviewing individual architectures, boards focus on standards development, pattern certification, and capability building. They invest in automation tools, reference architectures, and training programs that enable teams to build secure architectures independently.
Staffing models shift from dedicated reviewers to embedded experts. Organizations hire security architects who code and developers with security expertise. Career paths reward those who bridge domains. Performance metrics value enabling secure delivery over finding problems. This talent strategy creates professionals who integrate security with development rather than operating separately.
Funding models align with value delivery. Security architecture review receives investment based on its contribution to secure, rapid delivery rather than compliance checkboxes. Automation tools and embedded experts demonstrate ROI through reduced incidents and faster delivery. This economic alignment ensures sustainable support for modern governance approaches.
Cultural transformation underpins organizational changes. Leadership consistently messages that security enables innovation rather than constraining it. Success stories celebrate teams achieving both security and velocity. Failures become learning opportunities rather than blame exercises. This cultural foundation enables the trust necessary for distributed governance models.
Technology Enablers
Modern security architecture governance depends on technology platforms that automate validation, enable collaboration, and provide continuous insight. These platforms transform governance from document-based approval to code-based validation, from point-in-time review to continuous assurance.
Source code repositories provide the foundation for architecture as code. Git workflows enable version control, peer review, and automated validation of architectural decisions. Pull requests trigger security checks before merging changes. Branch protection rules enforce architectural standards. This code-centric approach makes architecture decisions explicit and auditable.
CI/CD pipelines integrate security architecture validation throughout delivery workflows. Build stages validate that code follows secure patterns. Test stages confirm security controls function correctly. Deployment gates ensure only compliant architectures reach production. This pipeline integration makes security architecture governance a natural part of delivery rather than a separate process.
Policy engines translate security architecture standards into executable rules. Open Policy Agent and similar tools enable policy-as-code for infrastructure, applications, and APIs. Policies validate everything from network configurations to API schemas. This automation ensures consistent enforcement while enabling rapid feedback.
Observability platforms provide runtime validation of architectural security. Distributed tracing reveals actual service interactions for comparison with intended architectures. Security information and event management systems confirm control effectiveness. These operational insights validate that architectures deliver intended security outcomes.
Collaboration platforms enable distributed teams to coordinate security architecture decisions. Architecture decision records in wikis document choices and rationale. Diagramming tools with version control track architecture evolution. Virtual whiteboarding enables remote design sessions. These tools support the human aspects of distributed governance.
Analytics platforms synthesize data from across the technology stack to provide architecture insights. Machine learning identifies unusual patterns suggesting architectural drift. Dashboards visualize architecture compliance across portfolios. Predictive models anticipate future architectural risks. These insights enable proactive governance rather than reactive review.
Process Integration
Integrating security architecture governance with agile processes requires careful choreography. Success depends on adding security value without adding friction, enhancing delivery rather than impeding it. This integration happens through thoughtful process design that respects both security needs and agile principles.
Definition of ready criteria incorporate security architecture requirements. Before teams begin implementation, they confirm necessary security patterns are identified, architectural risks are understood, and required security controls are defined. This proactive approach prevents security surprises during development.
Definition of done includes security architecture validation. Teams cannot consider work complete until automated checks pass, security tests succeed, and architectural compliance is confirmed. This integration ensures security architecture requirements receive the same attention as functional requirements.
Incremental review approaches match agile's iterative nature. Rather than reviewing complete architectures, boards review incremental changes. Each sprint's architectural modifications receive appropriate scrutiny. This incremental approach enables continuous delivery while maintaining governance oversight.
Fast-track processes handle standard patterns. Pre-approved architectural patterns bypass detailed review when properly implemented. Teams following reference architectures proceed with automated validation only. This acceleration rewards adherence to standards while focusing human review on novel situations.
Exception handling provides flexibility within governance. Clear processes exist for deviating from architectural standards when justified. Risk-based approval authorities enable rapid decisions. Time-bound exceptions allow progress while planning standard compliance. This flexibility prevents governance from becoming rigid impediment.
Continuous process improvement refines integration over time. Regular retrospectives identify friction points in security architecture governance. Metrics track cycle times and bottlenecks. Feedback from teams drives process refinement. This improvement orientation ensures processes evolve with changing needs.
Case Studies and Lessons Learned
Financial Services: Automated Compliance at Scale
A major international bank transformed its security architecture review process to support agile delivery while maintaining regulatory compliance. Starting with traditional monthly review boards and multi-week approval cycles, the bank recognized this approach incompatible with digital transformation goals.
The transformation began with policy-as-code implementation. Security architects translated existing standards into automated rules for infrastructure and application validation. Terraform policies enforced network segmentation requirements. Container policies mandated encryption and access controls. API definitions included security schemas. This automation codified years of security architecture expertise.
Embedded security architects joined critical product teams. Rather than reviewing designs after the fact, these architects participated in design sessions and sprint planning. They helped teams understand security requirements and identify compliant implementation patterns. This embedded model shifted security from constraint to enabler.
Reference architectures accelerated standard implementations. The bank developed secure patterns for common scenarios: customer authentication, payment processing, data analytics. Teams using these patterns received automatic approval, focusing human review on novel architectures. This approach balanced standardization with innovation.
Results exceeded expectations. Architecture review time dropped from average six weeks to under 24 hours for standard patterns. Security incidents related to architectural issues decreased by 73%. Development teams reported higher satisfaction with security processes. Regulators praised the automated audit trails and continuous compliance validation.
Key lessons emerged from this transformation. Executive sponsorship proved crucial for overcoming organizational resistance. Investment in automation tools paid dividends through reduced manual effort. Cultural change took longer than technical implementation but proved essential for sustained success. The bank's journey demonstrates that regulatory compliance and agile delivery can coexist through modern governance approaches.
Healthcare: Privacy-Integrated Architecture Governance
A healthcare technology company faced unique challenges integrating security architecture review with agile development. HIPAA requirements demanded strict privacy controls while market pressures required rapid feature delivery. Traditional review processes created unacceptable delays in bringing innovations to patient care.
The company pioneered integrated security and privacy architecture reviews. Rather than separate security and privacy assessments, unified reviews addressed both concerns simultaneously. Privacy impact assessments merged with threat modeling exercises. Security architects trained in privacy requirements, while privacy officers learned security architecture principles.
Automation focused on privacy-specific controls. Tools validated that personal health information remained encrypted throughout data flows. Access control policies enforced minimum necessary standards. Audit logging met regulatory requirements automatically. This automation ensured consistent privacy protection without manual verification.
Agile teams included privacy champions alongside security champions. These dual roles ensured both security and privacy considerations influenced architectural decisions. Sprint planning included privacy user stories. Definition of done required privacy control validation. This integration made privacy a development concern rather than compliance afterthought.
Modular architecture approaches enhanced both security and privacy. Microservices isolated personal health information processing. API gateways enforced consent management. Encryption services centralized key management. This architectural modularity simplified both governance and implementation.
Outcomes validated the integrated approach. Time to market for new features improved by 40% compared to traditional review processes. Privacy incidents decreased despite faster delivery. Regulatory audits found strong privacy-by-design implementation. Patient trust scores increased as privacy features became product differentiators.
Critical insights guide others pursuing similar integration. Privacy and security architecture reviews share more commonalities than differences. Automation can address privacy requirements as effectively as security controls. Embedded expertise works for privacy as well as security. Healthcare's stringent requirements prove that integrated governance can work in any industry.
Technology Sector: Platform-Driven Governance
A cloud services provider revolutionized security architecture governance through platform engineering. Serving thousands of development teams building on their infrastructure, traditional review approaches could never scale. The company needed governance that operated at platform speed and scale.
Platform capabilities embedded security architecture standards. Default configurations implemented approved patterns. Guard rails prevented insecure architectures. Self-service tools enabled teams to build securely without understanding underlying complexity. The platform became the security architecture review board.
Developer experience drove governance design. Security requirements surfaced through intuitive interfaces. Error messages explained security issues and suggested fixes. Documentation integrated security guidance with implementation examples. This developer focus ensured security architecture governance enhanced rather than hindered productivity.
Continuous validation operated at massive scale. Every configuration change triggered automated security checks. Runtime monitoring verified architectural compliance across millions of resources. Machine learning identified anomalous patterns suggesting security issues. This continuous approach caught architectural drift before it became vulnerabilities.
Community contribution improved platform governance. Development teams suggested new security patterns based on their needs. Security architects reviewed and certified community patterns. Popular patterns graduated into platform defaults. This crowdsourced approach scaled security architecture expertise beyond any central team.
Metrics demonstrated platform effectiveness. Teams using platform defaults experienced 90% fewer security incidents. Architecture review overhead effectively disappeared for standard patterns. Developer satisfaction with security processes reached all-time highs. The platform model proved that governance can enable rather than constrain.
Essential learnings inform platform-based governance strategies. Platform investment requires long-term commitment but delivers exponential returns. Developer experience determines governance adoption more than policy mandates. Community contribution scales security expertise beyond organizational boundaries. Platform-driven governance represents the future for organizations operating at scale.
Future Evolution
Emerging Technologies and Their Impact
Artificial intelligence transforms security architecture governance in multiple dimensions. AI-powered tools analyze architectures for security weaknesses faster than human reviewers. Machine learning models predict architectural vulnerabilities based on historical patterns. Natural language processing extracts architectural decisions from documentation and code. These capabilities augment human expertise rather than replacing it.
Quantum computing threatens current cryptographic architectures while enabling new security capabilities. Security architecture review boards must plan for quantum-resistant algorithms and hybrid classical-quantum systems. Architecture governance processes need frameworks for evaluating quantum readiness and migration strategies. Early preparation prevents future architectural overhauls.
Edge computing distributes architectures beyond traditional boundaries. Security governance must address devices, locations, and networks outside direct control. Zero trust principles become essential rather than optional. Architecture reviews consider partial connectivity, limited computing resources, and physical security threats. Edge architectures require governance evolution.
Blockchain and distributed ledger technologies introduce new architectural patterns. Decentralized trust models challenge traditional security architectures. Smart contract vulnerabilities require specialized review expertise. Consensus mechanisms impact performance and security tradeoffs. Architecture governance must understand and address these novel patterns.
5G networks enable architectures previously impossible due to latency or bandwidth constraints. Network slicing provides architectural isolation opportunities. Mobile edge computing brings processing closer to users. These capabilities require security architecture governance that understands network evolution. Traditional perimeter-based thinking becomes obsolete.
Evolving Threat Landscape
Supply chain attacks target architectural dependencies. Security architecture review must examine not just direct implementations but entire dependency trees. Software bill of materials becomes architectural documentation. Governance processes verify component integrity and monitor for compromises. Architecture reviews extend beyond organizational boundaries.
AI-powered attacks exploit architectural patterns. Adversarial machine learning targets AI-based security controls. Automated reconnaissance maps architectures for weaknesses. Social engineering uses architectural knowledge for targeted attacks. Security architecture governance must anticipate intelligent adversaries.
Ransomware evolution drives architectural resilience requirements. Immutable backups, network segmentation, and identity isolation become architectural imperatives. Recovery time objectives influence architectural decisions. Business continuity merges with security architecture. Governance ensures architectures support both prevention and recovery.
Privacy regulations expand architectural requirements globally. Data sovereignty drives geographic architectural decisions. Consent management requires architectural support. Right to deletion impacts data architecture fundamentally. Security architecture governance increasingly addresses privacy alongside traditional security.
Organizational Transformation
Digital transformation accelerates, demanding faster architectural evolution. Business models pivot rapidly, requiring architectural agility. Customer expectations for features and security increase simultaneously. Technology becomes business strategy rather than support function. Security architecture governance must enable business transformation.
Workforce changes impact governance models. Remote work permanence requires distributed governance approaches. Gig economy participation demands rapid onboarding and offboarding architectures. Generation differences in technology comfort influence governance design. Human factors become central to architectural security.
Ecosystem business models blur organizational boundaries. Partner integrations require federated governance models. API economies demand standardized security patterns. Platform strategies need scalable governance approaches. Security architecture review extends across organizational networks.

Conclusion and Recommendations
Security architecture review boards stand at an inflection point. Traditional approaches that served the industry for decades no longer match modern delivery realities. Agile methodologies, DevSecOps practices, and continuous delivery demand governance evolution. Organizations clinging to heavyweight review processes find themselves bypassed, becoming impediments rather than enablers.
Yet the need for security architecture governance has never been greater. Sophisticated threats, complex regulations, and interconnected systems require thoughtful architectural security. Design decisions have lasting impact on organizational security posture. Architectural vulnerabilities create systemic risks that point solutions cannot address.
The path forward requires embracing fundamental changes in how security architecture review boards operate. Embedded expertise brings security knowledge directly into development teams. Automation enables governance at the speed of delivery. Agile integration makes security architecture a natural part of development flow. Adaptive models match governance intensity to risk. Continuous validation ensures architectures remain secure as they evolve.
Success requires commitment across multiple dimensions. Leadership must champion governance transformation, providing resources and removing obstacles. Technology investments in automation and platforms enable scalable governance. Process changes integrate security throughout delivery lifecycles. Cultural shifts position security as innovation enabler rather than business constraint.
Organizations beginning this journey should start with pilot implementations. Select willing teams and supportive leaders for initial transformation. Demonstrate value through faster delivery and improved security. Build success stories that inspire broader adoption. Learn from failures without abandoning the vision. Iterate approaches based on experience.
The future belongs to organizations that master secure agile delivery. Those that successfully transform security architecture governance gain competitive advantage through both speed and safety. They deliver innovations rapidly while maintaining customer trust. They navigate regulations confidently while embracing change. They build the secure, agile architectures that tomorrow's challenges demand.
Security architecture review boards that evolve will thrive. Those that resist will become irrelevant. The choice is clear, the path is proven, and the time is now. Organizations must act decisively to transform security architecture governance for the agile age. The principles exist, the technologies enable, and the benefits await. The only question remaining is whether organizations will seize this opportunity or let it pass.
The journey from traditional review boards to modern security architecture governance is neither simple nor swift. It requires sustained commitment, continuous learning, and willingness to challenge established practices. But organizations that complete this transformation discover something powerful: security architecture governance that enables rather than constrains, that accelerates rather than delays, that builds trust rather than compliance checkboxes.
This is the future of security architecture review boards: embedded in teams, automated in pipelines, integrated with development, adaptive to risk, and continuously improving. Organizations that embrace these principles position themselves for success in an increasingly complex and rapidly evolving technology landscape. The time for transformation is now.
Stay safe, stay secure.
The CybersecurityHQ Team
Reply