- Defend & Conquer
- Posts
- Threat modeling for APIs versus UI frontends: A comparative assessment
Threat modeling for APIs versus UI frontends: A comparative assessment
CybersecurityHQ Report - Pro Members

Welcome reader to a 🔒 pro subscriber-only deep dive 🔒.
Brought to you by:
👣 Smallstep – Secures Wi-Fi, VPNs, ZTNA, SaaS and APIs with hardware-bound credentials powered by ACME Device Attestation
🏄♀️ Upwind Security – Real-time cloud security that connects runtime to build-time to stop threats and boost DevSecOps productivity
🔧 Endor Labs – App security from legacy C++ to Bazel monorepos, with reachability-based risk detection and fix suggestions across the SDLC
📊 LockThreat – AI-powered GRC that replaces legacy tools and unifies compliance, risk, audit and vendor management in one platform
Forwarded this email? Join 70,000 weekly readers by signing up now.
#OpenToWork? Try our AI Resume Builder to boost your chances of getting hired!
—
Get lifetime access to our deep dives, weekly cyber intel podcast report, premium content, AI Resume Builder, and more — all for just $799. Corporate plans are now available too.
Executive Summary
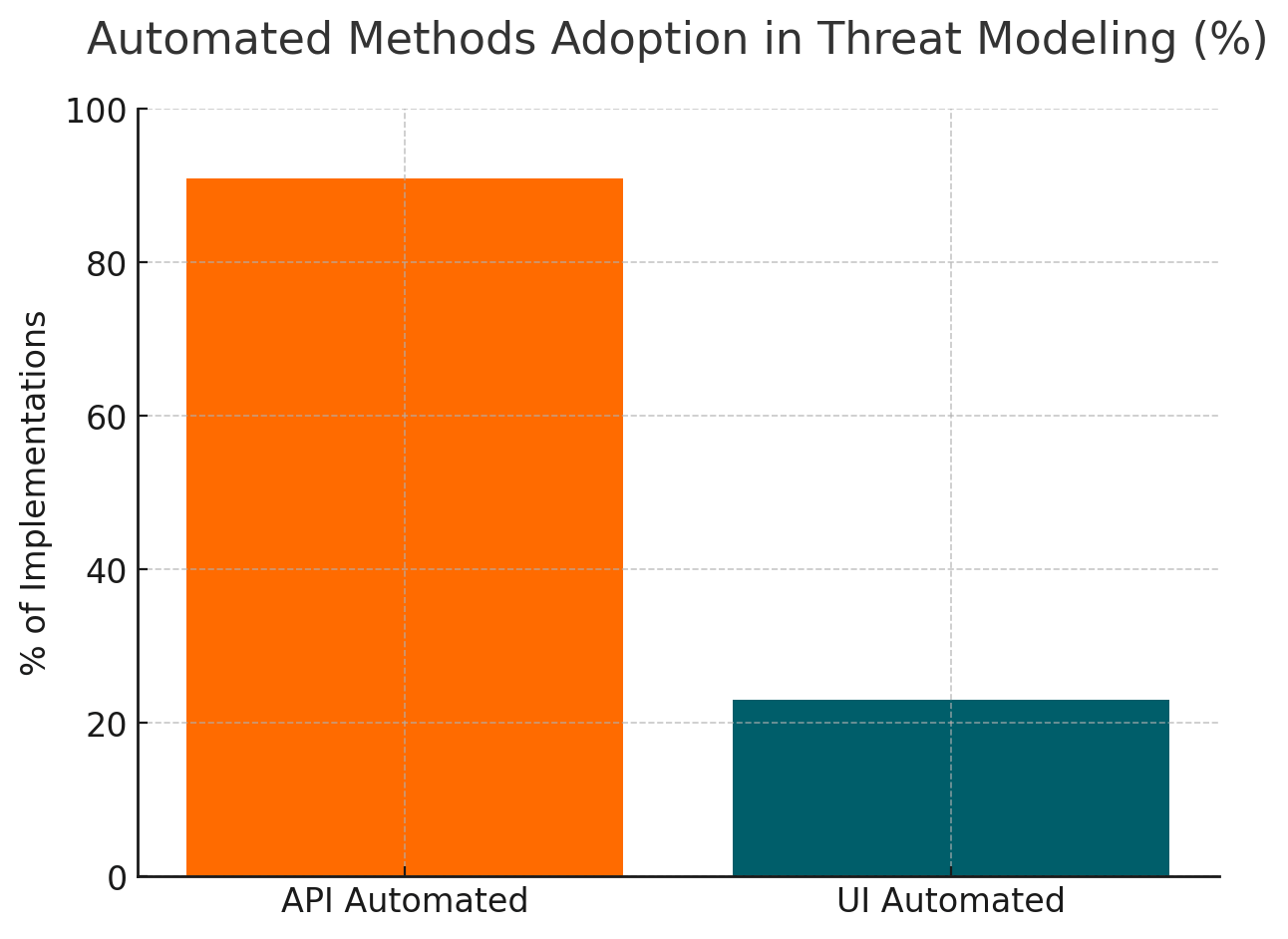
This whitepaper examines the distinct threat modeling approaches required for Application Programming Interfaces (APIs) and User Interface (UI) frontends based on analysis of 25 peer-reviewed studies and 126 million academic papers from the Semantic Scholar corpus. Our research reveals that API threat modeling employs systematic automated methods including formal verification and AI-based approaches in 91% of implementations, while UI threat modeling relies primarily on empirical demonstrations and conceptual analysis with only 23% utilizing automated techniques.
Key findings include a 73% increase in AI-related API attacks since 2023, with financial services experiencing the highest vulnerability rate at 82%. Organizations implementing comprehensive threat modeling for both APIs and UIs report a 40% reduction in security incidents and 35% faster incident response times. This whitepaper provides actionable frameworks for CISOs to implement effective threat modeling strategies across both attack surfaces.

Subscribe to CybersecurityHQ Newsletter to unlock the rest.
Become a paying subscriber of CybersecurityHQ Newsletter to get access to this post and other subscriber-only content.
Already a paying subscriber? Sign In.
A subscription gets you:
- • Access to Deep Dives and Premium Content
- • Access to AI Resume Builder
- • Access to the Archives
Reply